Bitwarden Web Vault. The project that was releasing the packages for debian doesn't ship them anymore but just release the files and instructions to package it on my own. Someone knows if there is a public repository for Debian with packages already built? I don't have time and resources to generate on my own.
Bitwarden Inactive 2fa Report
This article is part of the series Build your very own self-hosting platform with Raspberry Pi and Kubernetes
- Self-host your password manager with Bitwarden
Introduction
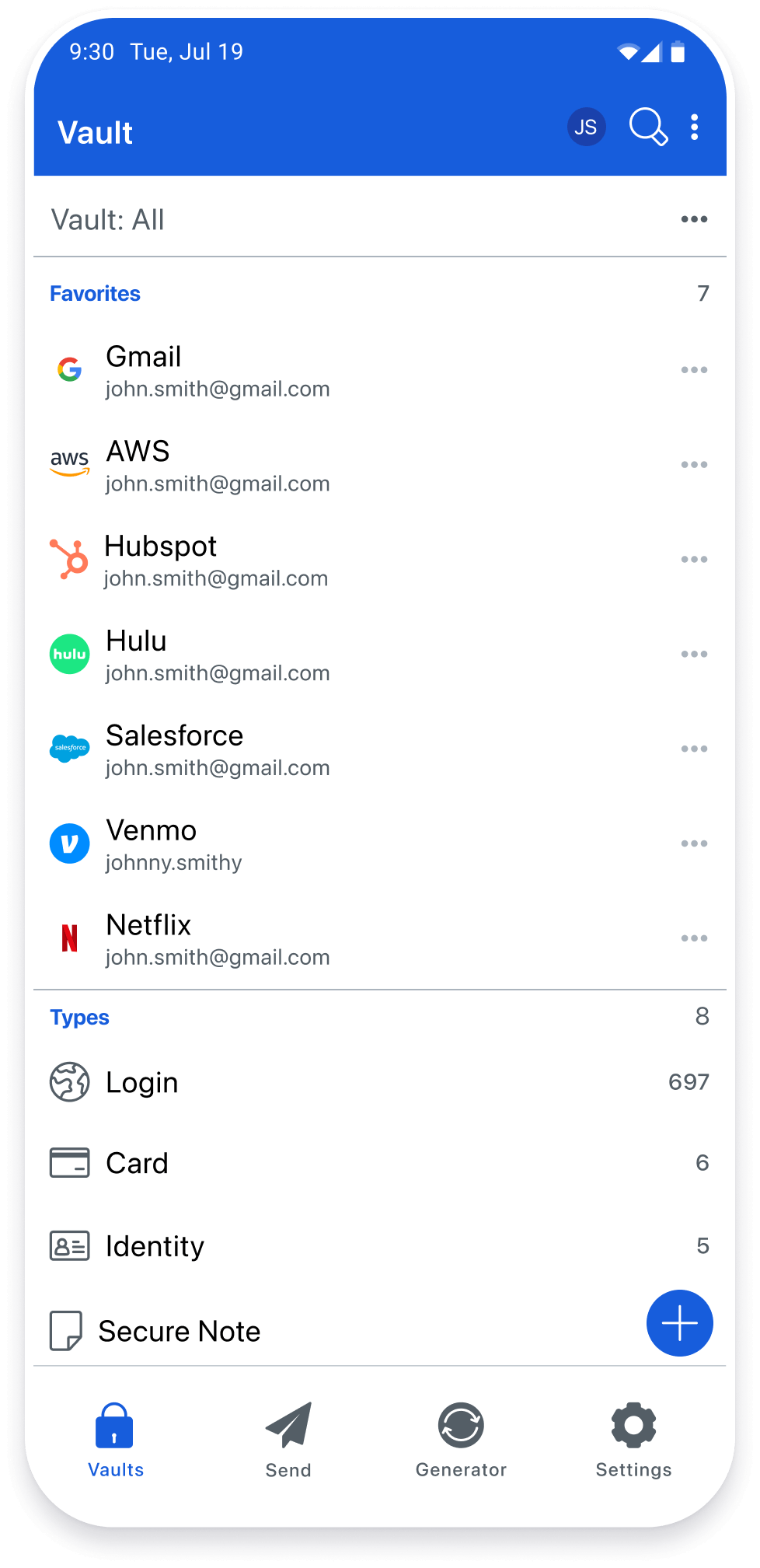
Bitwarden is a free, open-source and audited Password Manager, it provides a large range of clients (desktop, web, browser extension and mobiles) to access your password easily and safely from anywhere. Lg mobile phones & portable devices driver download. While Bitwarden offers a SaaS solutions (they host your passwords in an encrypted way), because Bitwarden is open-source, you can decide to host yourself your password and this is what we are going to learn in this tutorial.
For information, we will deploy Bitwarden-rs, Unofficial Bitwarden compatible server written in Rust, ideal for self-hosting.
This is a Bitwarden server API implementation written in Rust compatible with upstream Bitwarden clients*, perfect for self-hosted deployment where running the official resource-heavy service might not be ideal. This project is not associated with the Bitwarden project nor 8bit Solutions LLC.
Prerequisite
In order to run entirely the tutorial, we will need:
- A running Kubernetes cluster (see previous articles if you haven't set this up yet)
- A domain name in order to access our Bitwarden instance from outside our network. (replace
<domain.com>by your domain) - Have a external static IP (usually the case by default)
- Access to your router admin console to port-forward an incoming request to our Kubernetes Ingress service.
Namespace
We are going to isolate all the Kubernetes objects related to Bitwarden in the namespace bitwarden.
To create a namespace, run the following command:
Persistence
The first step consists in setting up a volume to store Bitwarden config files and data. Drivers j2 retail laptops & desktops. If you followed the previous articles to install and configure a self-hosting platform using RaspberryPi and Kubernetes, you remember we have on each worker a NFS client pointing to a SSD on /mnt/ssd.
1. Deploy the Persistent Volume (PV)
The Persistent Volume specify the name, the size, the location and the access modes of the volume:
- The name of the PV is
bitwarden-ssd - The size allocated is 500MB
- The location is
/mnt/ssd/bitwarden - The access is ReadWriteOnce
Create the following file and apply it to the k8 cluster.
You can verify the PV exists with the following command:
2. Create the Persistent Volume Claim (PVC)
The Persistent Volume Claim is used to map a Persistent Volume to a deployment or stateful set. Unlike the PV, the PVC belongs to a namespace.
Create the following file and apply it to the k8 cluster.
You can verify the PVC exists with the following command:
Outside access
The next part consist to enable the connections to Bitwarden from outside so you can access your passwords from anywhere.
1. Port Forwarding
First you need to go to your router setup and add a port-forwarding rule to map any incoming requests on port 80 or port 443 to be forwarded to 192.168.0.240 (the LoadBalancer IP of the Nginx).
VirginHub - Port-Forwarding
2. Map the subdomain bitwarden.<domain.com> to your home router

First you need to find out what's your router external IP, run this command or go to whatismyip.com.
Then, we need to configure our subdomain to make sure bitwarden.<domain.com> resolves to our external static IP. Go to your domain provider console / DNS management add a record:
- Type: A
- Name: bitwarden (subdomain)
- Value: x.x.x.x (external static IP)
GoDaddy
Deployment
1. Clone the repo bitwarden-k8s
Clone the repository bitwarden-k8s with the following command (change ~/workspace/bitwarden-k8s by the target folder of your choice):

2. Download the Chart values of the chart locally
Run the following command to download the Chart values into the local file pihole.values.yml.
If you open the file, you will see the default configuration values to setup Bitwarden. Drivers medtronic others. Instead of using the flag --set property=value like before, we will use the file bitwarden.values.yml to make all the changes.
3. Update the values
We now need to update a few properties before installing the Helm chart. Open the file bitwarden.values.yml and change the following properties.
First we need to change to an ARM compatible image
Then we configure the environment variables.
Replace [ADMIN_TOKEN] by the result of the command $ openssl rand -base64 48. This token will be used to connect to the Bitwarden administration interface.
In the next step, we configure an ingress to access Bitwarden and issue a certificate (especially if we want to access from outside).
Replace <domain.com> by your domain (same as the section 'Internet access')
Finally, we want to plug Bitwarden to the persistent volume created at the beginning of the article pointing to /mnt/ssd/bitwarden.
4. Install the Chart
In the part, we will install the Helm chart under the namespace bitwarden with bitwarden.values.yml as configuration file.
After a couple of minutes, check if the pod and service is up and running:
Configuration
Once Bitwarden is up and running, we can start configuring our first user.
1. Access the admin interface
First, access the admin interface which should be available on /admin'>https://bitwarden.<domain.com>/admin and enter the <ADMIN_PASSWORD> generated previously.
2. Invite your first user
Once connected, you can check and modify the different parameters of Bitwarden and invite a new user. Enter an email address to invite a new user.
After a few seconds, You should received the invitation via email. Click on 'Join the Organisation'.
3. Create an account and login for the first time
Click on 'Create Account'.
Configure the details of the user: name, master password (encryption key) and click on 'Submit'.
Finally, log into with the newly created user using the couple email, master password.
Conclusion
You now have a fully self-hosted password manager accessible via your own domain from anywhere.
You can also install and configure your custom server to easily and safely access your password:
- Bitwarden Mobile App (available on iOS and GooglePlay)
- Bitwarden Web Browser extension (available on Chrome and Firefox)
- Kauri original title: (7/8) Self-host your password manager with Bitwarden
- Kauri original link: https://kauri.io/78-selfhost-your-password-manager-with-bitwarden/b2187730d4294626b28d1d938057e2e0/a
- Kauri original author: Grégoire Jeanmart (@gregjeanmart)
- Kauri original Publication date: 2020-04-01
- Kauri original tags: self-hosting, kubernetes, password-manager, bitwarden
- Kauri original hash: QmdEAA7UJgWkx9FgUiRXnEJuE46chrd7S9R4j9w78gL6ka
- Kauri original checkpoint: unknown
Bitwarden Security Report
Bitwarden Rpm Repo
Solve your password management problems
The easiest and safest way for individuals, teams, and business organizations to store, share, and sync sensitive data
YOUR ONLINE SAFETY IS AT RISK
Password theft is a serious problem. The websites and apps that you use are under attack every day. Security breaches occur and your passwords are stolen. When you reuse the same passwords everywhere hackers can easily access your email, bank, and other important accounts.
HOW DO YOU STAY SAFE?
Security experts recommend that you use a different, randomly generated password for every online account that you create. But how are you supposed to remember and keep up with that many passwords? Bitwarden helps you create and manage secure passwords so that you can get back to enjoying your life online.
[ QPKG Integration] - Based on BitWarden_rs
use port 8000
disable all ADBlock on webrowser (or create rules)
prefix install : /opt/Bitwarden
Note: building the Vault needs ~1.5GB of RAM. On systems like a RaspberryPI with 1GB or less, please enable swapping or build it on a more powerful machine and copy the directory from there. This much memory is only needed for building it, running bitwarden_rs with vault needs only about 10MB of RAM
BUY IT NOW
Your gratitude and finance will help me to continue integration of this QPKG and maintain up to date versions.
Greetings to
dani-garcia : https://github.com/dani-garcia/bitwarden_rs/
