Mar 20, 2020 hq-vpn-headend# show vpn-sessiondb anyconnect Session Type: AnyConnect Username: santaclaus Index: 1 Assigned IP: 192.168.46.5 Public IP: 10.254.8.19 Protocol: AnyConnect-Parent SSL-Tunnel DTLS-Tunnel License: AnyConnect Premium Encryption: AnyConnect-Parent: (1)none SSL-Tunnel: (1)AES-GCM-256 DTLS-Tunnel: (1)AES256 Hashing: AnyConnect. The none default anyconnect part tells the ASA not to ask the user if he/she wants to use WebVPN or anyconnect but just starts the download of the anyconnect client automatically. The anyconnect dpd-interval command is used for Dead Peer Detection. On the ASA you have the option to deploy/update AnyConnect VPN module and the ISE Posture, but there is no option to deploy/update the ISE Compliance Module. Upon inital connection to the VPN if the ASA has a newer AnyConnect package the client will auto-update AnyConnect from the ASA - this is before the ISE Posture agent has communicated to ISE.
The LoginTC RADIUS Connector is a complete two-factor authentication virtual machine packaged to run within your corporate network. The LoginTC RADIUS Connector enables Cisco ASA to use LoginTC for the most secure two-factor authentication. For instructions using direct authentication then you may be interested in: Two factor authentication for Cisco ASA SSL VPN.
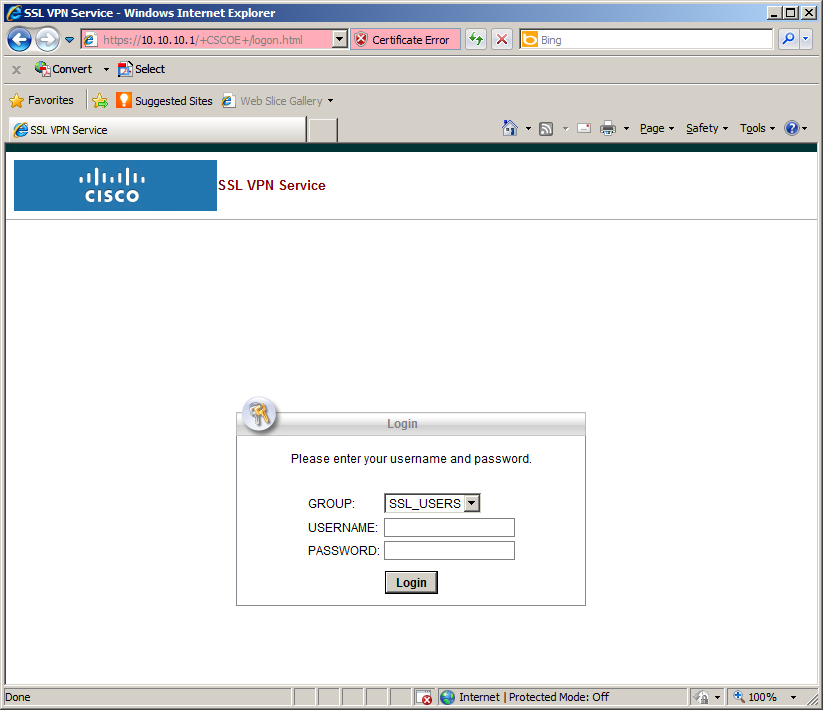
User Experience
After entering the username and password into the AnyConnect client, the user is presented with an Authentication Message. The user may enter ‘1’ to receive a push notification to their device to approve or enter a valid One-Time Password (OTP). This flow works the same for clientless access.
Video Instructions
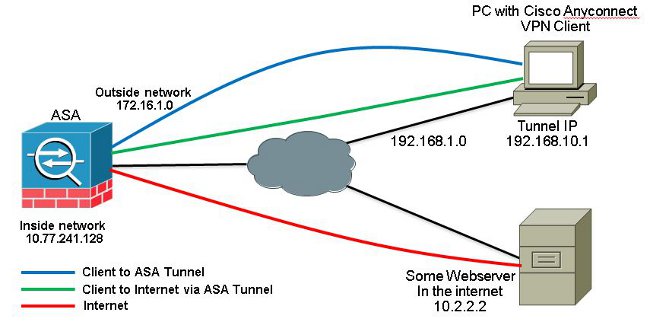
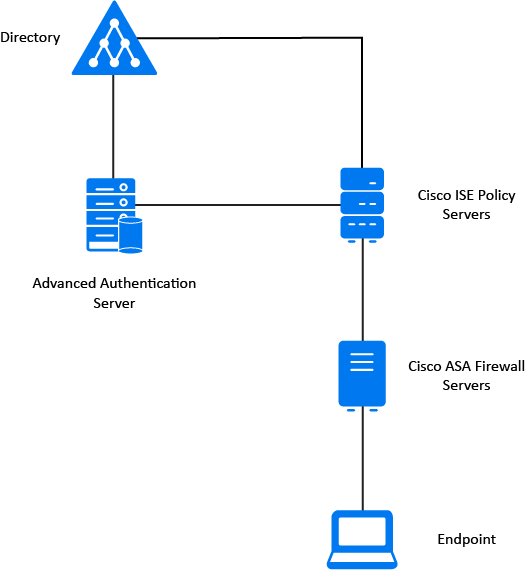
Architecture
Authentication Flow
- A user attempts access with their existing Cisco AnyConnect client with username / password
- A RADIUS authentication request is sent to the LoginTC RADIUS Connector
- The username / password is verified against an existing first factor directory (LDAP, Active Directory or RADIUS)
- An authentication request is made to LoginTC Cloud Services
- Secure push notification request sent to the user’s mobile or desktop device
- User response (approval or denial of request) sent to LoginTC Cloud Services
- The LoginTC RADIUS Connector polls until the user responds or a timeout is reached
- RADIUS Access-Accept sent back to Cisco ASA
- User is granted access to Cisco ASA
Prefer Reading a PDF?
Download a PDF file with configuration instructions for your chosen VPN protocol:
Compatibility
Cisco ASA appliance compatibility:
- Cisco ASA 5505
- Cisco ASA 5506-X Series
- Cisco ASA 5508-X
- Cisco ASA 5510-X
- Cisco ASA 5512-X
- Cisco ASA 5515-X
- Cisco ASA 5516-X
- Cisco ASA 5525-X
- Cisco ASA 5545-X
- Cisco ASA 5555-X
- Cisco ASA 5585-X Series
- Cisco appliance supporting RADIUS authentication
Appliance not listed?
We probably support it. Contact us if you have any questions.
Compatibility Guide
Any other Cisco appliance which have configurable RADIUS authentication are supported.
Prerequisites
Before proceeding, please ensure you have the following:
- LoginTC Admin Panel account
- Computer virtualization software such as VMware ESXi, VirtualBox, or Hyper-V
- Virtual Machine requirements:
- 1024 MB RAM
- 8 GB disk size
Create Application
Start by creating a LoginTC Application for your deployment. An Application represents a service (e.g. An application is a service (e.g., VPN or web application) that you want to protect. e) that you want to protect with LoginTC.
Create a LoginTC Application in LoginTC Admin Panel, follow Create Application Steps.
If you have already created a LoginTC Application for your deployment, then you may skip this section and proceed to Installation.
Installation
- Download the latest LoginTC RADIUS Connector:
- Unzip the file
- Import the virtual appliance your computer virtualization software
- Ensure that the LoginTC RADIUS Connector has a virtual network card
- Start the virtual appliance
- You will be presented with a console dashboard:
- The first thing you must do is set the
logintc-userpassword: - By default the appliance network is configured by DHCP. If you wish to manually configure the network, use the Down arrow key to navigate to Network Configuration and DNS Configuration
- For access to the web interface select Web Server and then Start: It may take 5-10 seconds to start the first time:
- Once started, access the web interface by navigating to the URL mentioned in the information box:
Asa Cisco Anyconnect Student
The LoginTC RADIUS Connector runs CentOS 7.7 with SELinux. A firewall runs with the following open ports:
| Port | Protocol | Purpose |
|---|---|---|
| 22 | TCP | SSH access |
| 1812 | UDP | RADIUS authentication |
| 1813 | UDP | RADIUS accounting |
| 8888 | TCP | Web interface |
| 443 | TCP | Web interface |
| 80 | TCP | Web interface |
| 80 | TCP | Package updates (outgoing) |
| 123 | UDP | NTP, Clock synchronization (outgoing) |
Note: Username and Password
logintc-user is used for SSH and web access. The default password is logintcradius. You will be asked to change the default password on first boot of the appliance and will not be able to access the web interface unless it is changed.
The logintc-user has sudo privileges.
Configuration
Configuration describes how the appliance will authenticate your RADIUS-speaking device with an optional first factor and LoginTC as a second factor. Each configuration has 4 Sections:
1. LoginTC Ibm motherboards driver download for windows.
This section describes how the appliance itself authenticates against LoginTC Admin Panel with your LoginTC Application. Only users that are part of your organization and added to the domain configured will be able to authenticate.
2. First Factor
This section describes how the appliance will conduct an optional first factor. Either against an existing LDAP, Active Directory or RADIUS server. If no first factor is selected, then only LoginTC will be used for authentication.
3. Passthrough
This section describes whether the appliance will perform a LoginTC challenge for an authenticating user. The default is to challenge all users. However with either a static list or Active Directory / LDAP Group you can control whom gets challenged to facilitate seamless testing and rollout.
4. Client and Encryption
This section describes which RADIUS-speaking device will be connecting to the appliance and whether to encrypt API Key, password and secret parameters.
Data Encryption
It is strongly recommended to enable encryption of all sensitive fields for both PCI compliance and as a general best practice.
The web interface makes setting up a configuration simple and straightforward. Each section has a Test feature, which validates each input value and reports all potential errors. Section specific validation simplifies troubleshooting and gets your infrastructure protected correctly faster.
First Configuration
Close the console and navigate to your appliance web interface URL. Use username logintc-user and the password you set upon initial launch of the appliance. You will now configure the LoginTC RADIUS Connector.
Create a new configuration file by clicking + Create your first configuration:
LoginTC Settings
Configure which LoginTC Application to us:
Configuration values:
| Property | Explanation |
|---|---|
Application ID | The 40-character Application ID, retrieve Application ID |
Application API Key | The 64-character Application API Key, retrieve Application API Key |
Request Timeout | Number of seconds that the RADIUS connector will wait for |
The Application ID and Application API Key are found on the LoginTC Admin Panel.
Request Timeout
Make a note of what you set the Request Timeout to as you will need to use a larger timeout value in your Cisco ASA. We recommend setting the Request Timeout value to 60 seconds in the LoginTC RADIUS Connector and setting the RADIUS authentication server timeout to 70 seconds in Cisco ASA.
Asa Cisco Firewall
Click Test to validate the values and then click Next:
First Authentication Factor
Configure the first authentication factor to be used in conjunction with LoginTC. You may use Active Directory / LDAP or an existing RADIUS server. You may also opt not to use a first factor, in which case LoginTC will be the only authentication factor.

Active Directory / LDAP Option
Select Active Directory if you have an AD Server. For all other LDAP-speaking directory services, such as OpenDJ or OpenLDAP, select LDAP:
Configuration values:
| Property | Explanation | Examples |
|---|---|---|
host | Host or IP address of the LDAP server | ldap.example.com or 192.168.1.42 |
port (optional) | Port if LDAP server uses non-standard (i.e., 389/636) | 4000 |
bind_dn | DN of a user with read access to the directory | cn=admin,dc=example,dc=com |
bind_password | The password for the above bind_dn account | password |
base_dn | The top-level DN that you wish to query from | dc=example,dc=com |
attr_username | The attribute containing the user’s username | sAMAccountName or uid |
attr_name | The attribute containing the user’s real name | displayName or cn |
attr_email | The attribute containing the user’s email address | mail or email |
Group Attribute (optional) | Specify an additional user group attribute to be returned the authenticating server. | 4000 |
RADIUS Group Attribute (optional) | Name of RADIUS attribute to send back | Filter-Id |
LDAP Group (optional) | The name of the LDAP group to be sent back to the authenticating server. | SSLVPN-Users |
encryption (optional) | Encryption mechanism | ssl or startTLS |
cacert (optional) | CA certificate file (PEM format) | /opt/logintc/cacert.pem |
Click Test to validate the values and then click Next.
Existing RADIUS Server Option
If you want to use your existing RADIUS server, select RADIUS:
Configuration values:
| Property | Explanation | Examples |
|---|---|---|
host | Host or IP address of the RADIUS server | radius.example.com or 192.168.1.43 |
port (optional) | Port if the RADIUS server uses non-standard (i.e., 1812) | 1812 |
secret | The secret shared between the RADIUS server and the LoginTC RADIUS Connector | testing123 |
RADIUS Vendor-Specific Attributes
Common Vendor-Specific Attributes (VSAs) found in the FreeRADIUS dictionary files will be relayed.
Click Test to validate the values and then click Next.
Passthrough
Configure which users will be challenged with LoginTC. This allows you to control how LoginTC will be phased in for your users. This flexibility allows for seamless testing and roll out.
For example, with smaller or proof of concept deployments select the Static List option. Users on the static list will be challenged with LoginTC, while those not on the list will only be challenged with the configured First Authentication Factor. That means you will be able to test LoginTC without affecting existing users accessing your VPN.
For larger deployments you can elect to use the Active Directory or LDAP Group option. Only users part of a particular LDAP or Active Directory Group will be challenged with LoginTC. As your users are migrating to LoginTC your LDAP and Active Directory group policy will ensure that they will be challenged with LoginTC. Users not part of the group will only be challenged with the configured First Authentication Factor.
No Passthrough (default)
Select this option if you wish every user to be challenged with LoginTC.
Static List
Select this option if you wish to have a static list of users that will be challenged with LoginTC. Good for small number of users.
LoginTC challenge users: a new line separated list of usernames. For example:
Active Directory / LDAP Group
Select this option if you wish to have only users part of a particular Active Directory or LDAP group to be challenged with LoginTC. Good for medium and large number of users.
Configuration values:
| Property | Explanation | Examples |
|---|---|---|
LoginTC challenge auth groups | Comma separated list of groups for which users will be challenged with LoginTC | SSLVPN-Users or two-factor-users |
host | Host or IP address of the LDAP server | ldap.example.com or 192.168.1.42 |
port (optional) | Port if LDAP server uses non-standard (i.e., 389/636) | 4000 |
bind_dn | DN of a user with read access to the directory | cn=admin,dc=example,dc=com |
bind_password | The password for the above bind_dn account | password |
base_dn | The top-level DN that you wish to query from | dc=example,dc=com |
attr_username | The attribute containing the user’s username | sAMAccountName or uid |
attr_name | The attribute containing the user’s real name | displayName or cn |
attr_email | The attribute containing the user’s email address | mail or email |
encryption (optional) | Encryption mechanism | ssl or startTLS |
cacert (optional) | CA certificate file (PEM format) | /opt/logintc/cacert.pem |
Configuration Simplified
If Active Directory / LDAP Option was selected in First Authentication Factor the non-sensitive values will be pre-populated to avoid retyping and potential typos.
Click Test to validate the values and then click Next.
Client and Encryption
Configure RADIUS client (e.g. your RADIUS-speaking VPN):
Client configuration values:
| Property | Explanation | Examples |
|---|---|---|
name | A unique identifier of your RADIUS client | CorporateVPN |
ip | The IP address of your RADIUS client (e.g. your RADIUS-speaking VPN) | 192.168.1.44 |
secret | The secret shared between the LoginTC RADIUS Connector and its client | bigsecret |
Under Authentication Mode select Challenge
The user will be prompted on how they wish to proceed with second-factor authentication (e.g. LoginTC Push, OTP, bypass code). Your RADIUS client must support RADIUS challenges to use this. Challenging the user will often result in a better user experience. See User Experience for more information.
Data Encryption
It is strongly recommended to enable encryption of all sensitive fields for both PCI compliance and as a general best practice.
Click Test to validate the values and then click Save.
Testing
When you are ready to test your configuration, create a LoginTC user (if you haven’t already done so). The username should match your existing user. Provision a token by following the steps:
- In a new tab / window log into the LoginTC Admin Panel
- Click Domains
- Click on your domain
- Click on Members
- Click Issue Token button beside your user:
- A 10-character alphanumeric activation code will appear beside the user:
- Open the LoginTC mobile app.
- Enter the 10-character alphanumeric activation code:
- Load the token to complete the process
When you have loaded a token for your new user and domain, navigate to your appliance web interface URL:
Click Test Configuration:
Enter a valid username and password; if there is no password leave it blank. A simulated authentication request will be sent to the mobile or desktop device with the user token loaded. Approve the request to continue:
Congratulations! Your appliance can successfully broker first and second factor authentication. The only remaining step is to configure your RADIUS device!
If there was an error during testing, the following will appear:
In this case, click See logs and then click the /var/log/logintc/authenticate.log tab to view the log file and troubleshoot:
Cisco ASA Configuration - Quick Guide
Once you are satisfied with your setup, configure your Cisco ASA client to use the LoginTC RADIUS Connector.
For your reference, the appliance web interfaceSettings page displays the appliance IP address and RADIUS ports:
The following are quick steps to protect your clientless and AnyConnect VPN setups with LoginTC. The instructions (tailored for Cisco ASA AnyConnect 2.5) can be used for existing setups as well.
- Launch your Cisco ASA ASDM
- Click AAA Local Users:
Under AAA Server Groups click Add:
Property Explanation Example Accounting ModeIndicates how accounting messages are sent. Recommended single mode. single modeReactivation ModeSpecifies the method by which failed servers are reactivated. depletedDead TimeTime for which a RADIUS server is skipped over by transaction requests 10Max Failed AttemptsMaximum number of retransmission attempts. Recommended 1. 1- Select Protocol: RADIUS
- Click Add
- Select the newly created group
Under Servers in the Selected Group click Add:
Property Explanation Example Interface NameName of protected Cisco interface insideServer name or IP AddressAddress of your LoginTC RADIUS Connector 192.168.1.7TimeoutAuthentication timeout. We recommend 70 seconds if you set the LoginTC Request timeout to 60 seconds. 70Server Authentication PortRADIUS authentication port. Must be 1812. 1812Server Accounting PortRADIUS accounting port. Must be 1813. 1813Retry IntervalLength of time between retries 5Server Secret KeyThe secret shared between the LoginTC RADIUS Connector and its client bigsecretMicrosoft CHAPv2 CapableWhether or not the RADIUS server uses CHAPv2. Must be unchecked - Click Clientless SSL VPN Access:
- Click Connection Profiles:
- Select DefaultWEBVPNGroup, click Edit:
- For the AAA Server Group select group made in steps 3-5
Click OK
Configure Timeout
By default, the Cisco AnyConnect client will timeout after 12 seconds on Windows and after 30 seconds on Mac OS X. Your users may require more time to authenticate, so the following steps will guide you in creating a profile to override the default timeout.
- Click on AnyConnect Client Profile
- Click the Add button
- Uncheck Auto Reconnect
- In the sidebar, click on Preferences(Cont) and scroll to the bottom
- Enter 80 for Authentication Timeout Values (or 10 seconds longer than the AAA RADIUS server timeout and 20 seconds longer than the LoginTC RADIUS Connector Request Timeout)
- Click OK
- In the sidebar, click on Server List
- Click on Add to add a server
- Enter the FQDN of your Cisco ASA VPN exposed end-point in the Hostname and a hostname or IP Address in the Host Address Click OK
- Click Apply
- Click on Group Policies under Network (Client) Access
- Click on the group policy that you have assigned to your VPN (e.g. DfltGrpPolicy)
- Under Advanced > AnyConnect Client Select your profile
To test, navigate to your Cisco ASA clientless VPN portal and attempt access.
Warning: Connection Timeouts
The new profile will be downloaded and applied only after you have successfully connected the first time. If you are having trouble with timeouts, we recommend that you connect using the clientless interface and clicking on the Start AnyConnect link to re-download the client. Also ensure that the FQDN and IP Address is correct in the Server List.
User Management
There are several options for managing your users within LoginTC:
- Individual users can be added manually in LoginTC Admin Panel
- Bulk operations using CSV Import
- Programmatically manage user lifecycle with the REST API
- One-way user synchronization of users to the LoginTC Admin is performed using User Sync Tool.
Troubleshooting
User Receives Multiple LoginTC Requests
See the Knowledge Base article for more information: My Cisco ASA AnyConnect SSL VPN users receive multiple LoginTC requests. What can I do?
Time Out After 12 Seconds
Ensure that you have configured the AnyConnect Client Profile. Also ensure that the profile Hostname is the same hostname that your end-users use to connect to the VPN.
Receiving Multiple Requests
Ensure that you have configured the AnyConnect Client Profile. Also ensure that the profile Hostname is the same hostname that your end-users use to connect to the VPN.
See the Knowledge Base article for more information: My Cisco ASA AnyConnect SSL VPN users receive multiple LoginTC requests. What can I do?
Not Authenticating
If you are unable to authenticate, navigate to your appliance web interface URL and click Status:
Ensure that all the status checks pass. For additional troubleshooting, click Logs:
Cisco Asa Anyconnect License
Email Support
For any additional help please email support@cyphercor.com. Expect a speedy reply.
Upgrading
From 3.X
Follow these instructions to upgrade your LoginTC RADIUS virtual appliance to the latest version (3.0.4):
- SSH into the virtual appliance or open the console (use same username / password as web GUI)
cd /tmpcurl -O https://www.logintc.com/downloads/logintc-radius-connector-3.0.4-upgrade.shsudo sh logintc-radius-connector-3.0.4-upgrade.sh
The upgrade script will restart your appliance after upgrading.
Upgrade Script Download Verification
Execute: sha1sum /tmp/logintc-radius-connector-3.0.4-upgrade.sh
Output SHA‑1 should match: d372582c6c8242de9cd4ce3e03e666fbd1cb20bb
From 2.X
Important: LoginTC RADIUS Connector 2.X End-of-life
The LoginTC RADIUS Connector 2.X virtual appliance is built with CentOS 6.8. CentOS 6.X is End of Lifetime (EOL) November 30th, 2020. See CentOS Product Specifications. Although the appliance will still function it will no longer receive updates and nor will it be officially supported.
New LoginTC RADIUS Connector 3.X
A new LoginTC RADIUS Connector 3.X virtual appliance has been created which runs CentOS 7.7.1908. It is virtually identical to the existing appliance, with the exception of the underlying operating system. Inline upgrade from CentOS 6.X to CentOS 7.X is not supported. As a result upgrade is deploying a new appliance. A migration script has been created to help quickly copy over existing configurations and ssl certificates to the new appliance and minimize manual steps.
Complete 2.X to 3.X upgrade guide: LoginTC RADIUS Connector Upgrade Guide
Additional Resources
 -->
-->In this tutorial, you'll learn how to integrate Cisco AnyConnect with Azure Active Directory (Azure AD). When you integrate Cisco AnyConnect with Azure AD, you can:
- Control in Azure AD who has access to Cisco AnyConnect.
- Enable your users to be automatically signed-in to Cisco AnyConnect with their Azure AD accounts.
- Manage your accounts in one central location - the Azure portal.
Prerequisites
To get started, you need the following items:
- An Azure AD subscription. If you don't have a subscription, you can get a free account.
- Cisco AnyConnect single sign-on (SSO) enabled subscription.
Scenario description
In this tutorial, you configure and test Azure AD SSO in a test environment.
- Cisco AnyConnect supports IDP initiated SSO
Adding Cisco AnyConnect from the gallery
To configure the integration of Cisco AnyConnect into Azure AD, you need to add Cisco AnyConnect from the gallery to your list of managed SaaS apps.
- Sign in to the Azure portal using either a work or school account, or a personal Microsoft account.
- On the left navigation pane, select the Azure Active Directory service.
- Navigate to Enterprise Applications and then select All Applications.
- To add new application, select New application.
- In the Add from the gallery section, type Cisco AnyConnect in the search box.
- Select Cisco AnyConnect from results panel and then add the app. Wait a few seconds while the app is added to your tenant.
Configure and test Azure AD SSO for Cisco AnyConnect
Configure and test Azure AD SSO with Cisco AnyConnect using a test user called B.Simon. For SSO to work, you need to establish a link relationship between an Azure AD user and the related user in Cisco AnyConnect.
To configure and test Azure AD SSO with Cisco AnyConnect, perform the following steps:
- Configure Azure AD SSO - to enable your users to use this feature.
- Create an Azure AD test user - to test Azure AD single sign-on with B.Simon.
- Assign the Azure AD test user - to enable B.Simon to use Azure AD single sign-on.
- Configure Cisco AnyConnect SSO - to configure the single sign-on settings on application side.
- Create Cisco AnyConnect test user - to have a counterpart of B.Simon in Cisco AnyConnect that is linked to the Azure AD representation of user.
- Test SSO - to verify whether the configuration works.
Configure Azure AD SSO
Follow these steps to enable Azure AD SSO in the Azure portal.
In the Azure portal, on the Cisco AnyConnect application integration page, find the Manage section and select single sign-on.
On the Select a single sign-on method page, select SAML.
On the Set up single sign-on with SAML page, click the edit/pen icon for Basic SAML Configuration to edit the settings.
On the Set up single sign-on with SAML page, enter the values for the following fields:
a. In the Identifier text box, type a URL using the following pattern:
< YOUR CISCO ANYCONNECT VPN VALUE >b. In the Reply URL text box, type a URL using the following pattern:
< YOUR CISCO ANYCONNECT VPN VALUE >Note
These values are not real. Update these values with the actual Identifier and Reply URL. Contact Cisco AnyConnect Client support team to get these values. You can also refer to the patterns shown in the Basic SAML Configuration section in the Azure portal.
On the Set up single sign-on with SAML page, in the SAML Signing Certificate section, find Certificate (Base64) and select Download to download the certificate file and save it on your computer.
On the Set up Cisco AnyConnect Drivers jooyon laptops & desktops. section, copy the appropriate URL(s) based on your requirement.
Note
If you would like to on board multiple TGTs of the server then you need to add multiple instance of the Cisco AnyConnect application from the gallery. Also you can choose to upload your own certificate in Azure AD for all these application instances. That way you can have same certificate for the applications but you can configure different Identifier and Reply URL for every application.
Create an Azure AD test user
In this section, you'll create a test user in the Azure portal called B.Simon.
- From the left pane in the Azure portal, select Azure Active Directory, select Users, and then select All users.
- Select New user at the top of the screen.
- In the User properties, follow these steps:
- In the Name field, enter
B.Simon. - In the User name field, enter the username@companydomain.extension. For example,
B.Simon@contoso.com. - Select the Show password check box, and then write down the value that's displayed in the Password box.
- Click Create.
- In the Name field, enter
Assign the Azure AD test user
In this section, you'll enable B.Simon to use Azure single sign-on by granting access to Cisco AnyConnect.
- In the Azure portal, select Enterprise Applications, and then select All applications.
- In the applications list, select Cisco AnyConnect.
- In the app's overview page, find the Manage section and select Users and groups.
- Select Add user, then select Users and groups in the Add Assignment dialog.
- In the Users and groups dialog, select B.Simon from the Users list, then click the Select button at the bottom of the screen.
- If you are expecting a role to be assigned to the users, you can select it from the Select a role dropdown. If no role has been set up for this app, you see 'Default Access' role selected.
- In the Add Assignment dialog, click the Assign button.
Configure Cisco AnyConnect SSO
You are going to do this on the CLI first, you might come back through and do an ASDM walk-through at another time.
Connect to your VPN Appliance, you are going to be using an ASA running 9.8 code train, and your VPN clients will be 4.6+.
First you will create a Trustpoint and import our SAML cert.
The following commands will provision your SAML IdP.
Now you can apply SAML Authentication to a VPN Tunnel Configuration.
Note
There is a feature with the SAML IdP configuration - If you make changes to the IdP config you need to remove the saml identity-provider config from your Tunnel Group and re-apply it for the changes to become effective.
Create Cisco AnyConnect test user
In this section, you create a user called Britta Simon in Cisco AnyConnect. Work with Cisco AnyConnect support team to add the users in the Cisco AnyConnect platform. Users must be created and activated before you use single sign-on.
Test SSO
In this section, you test your Azure AD single sign-on configuration with following options.
- Click on Test this application in Azure portal and you should be automatically signed in to the Cisco AnyConnect for which you set up the SSO
- You can use Microsoft Access Panel. When you click the Cisco AnyConnect tile in the Access Panel, you should be automatically signed in to the Cisco AnyConnect for which you set up the SSO. For more information about the Access Panel, see Introduction to the Access Panel.
Next Steps
Once you configure Cisco AnyConnect you can enforce session control, which protects exfiltration and infiltration of your organization’s sensitive data in real time. Session control extends from Conditional Access. Learn how to enforce session control with Microsoft Cloud App Security.
